20250815124514 - BLG - PhrackCTF2025 QR Decoding
Description
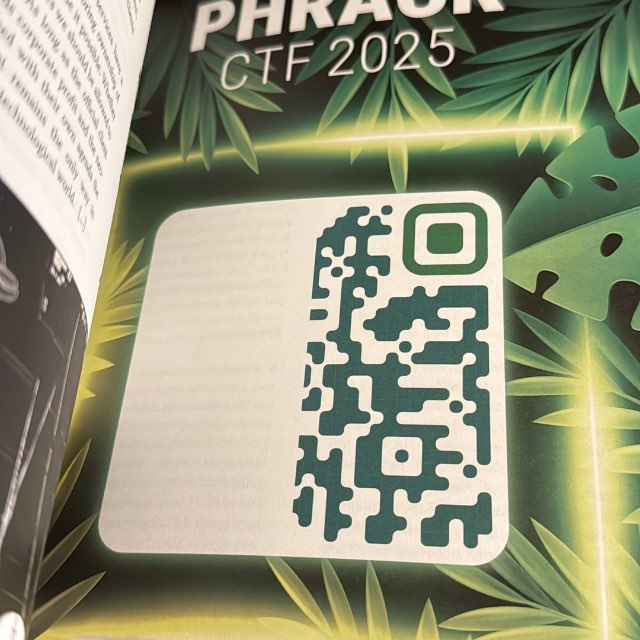
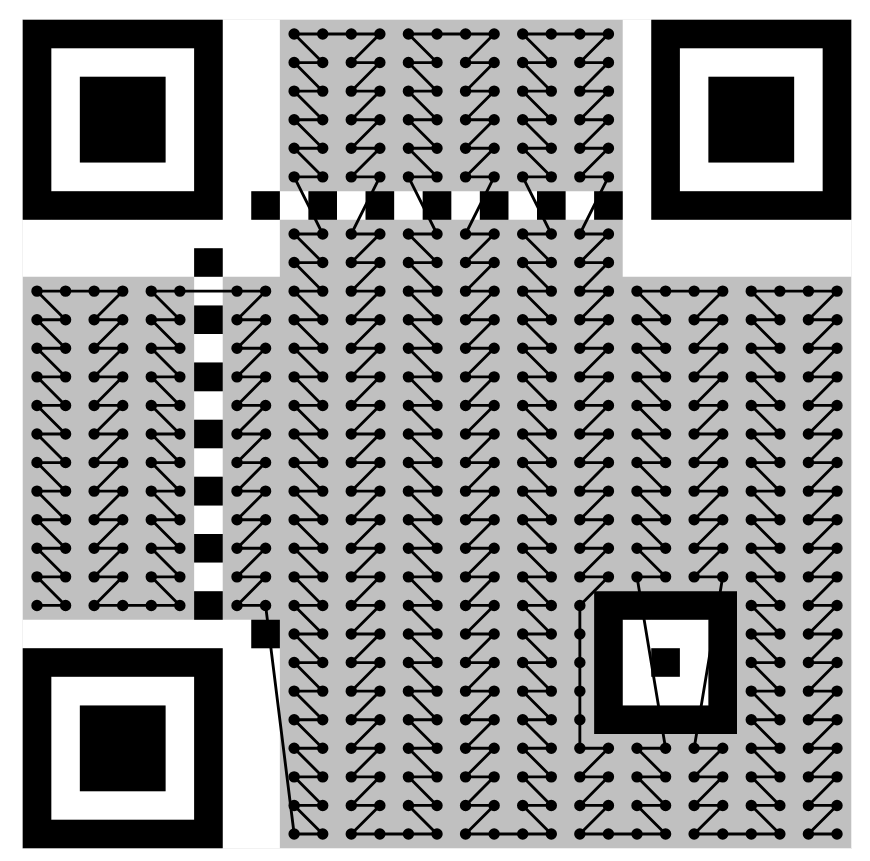
During Defcon, I have collected the Phrack Magazine on the same day I collected the Defcon 33 Badge. After seeing Chompie1337’s tweet, I realised that I have missed out on PhrackCTF2025. It seems that the original intent was to look for other people with a different copy of the distributed phrack magazine. But it was after Defcon that I realised and so I had to do things the hard way (decoding this QR code).
Decoding this QR Code
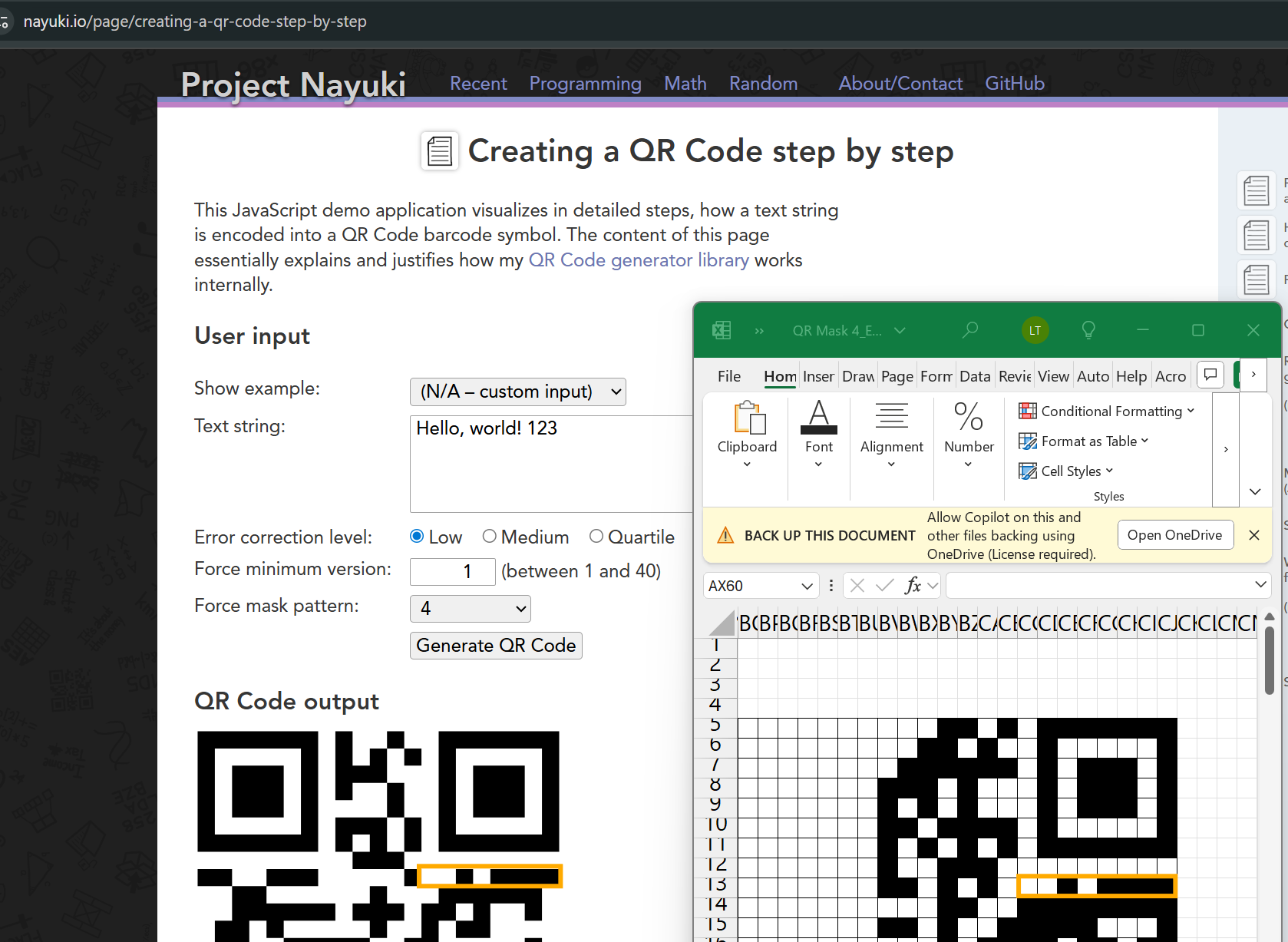
For this “challenge”, I decoded the link to the CTF with the help of Microsoft Excel. After watching numerous QR code generation tutorials, I have found a link (that I will link to if I find it again) that taught me how to decode. Fortunately, the half of the QR code contains all the necessary information there is to decode. If I have gotten the left side of things (Reed Solomon ECC), I would probably have given up.
What We Have?
On the left side, we have the error level and masking details. We also would have the length for the data. Of course, we have all the data on the right side (CTF platform link).
Microsoft Excel FTW!
The first thing is to recreate what we have! I have pasted the very same first image at the top to Affinity Designer to draw lines to keep my sanity intact. I then “encoded” line by line of the qrcode from the right most and bottom up.
For instance:
W1326131417......From there, it helped me to generate line by line more easily (yes manually). 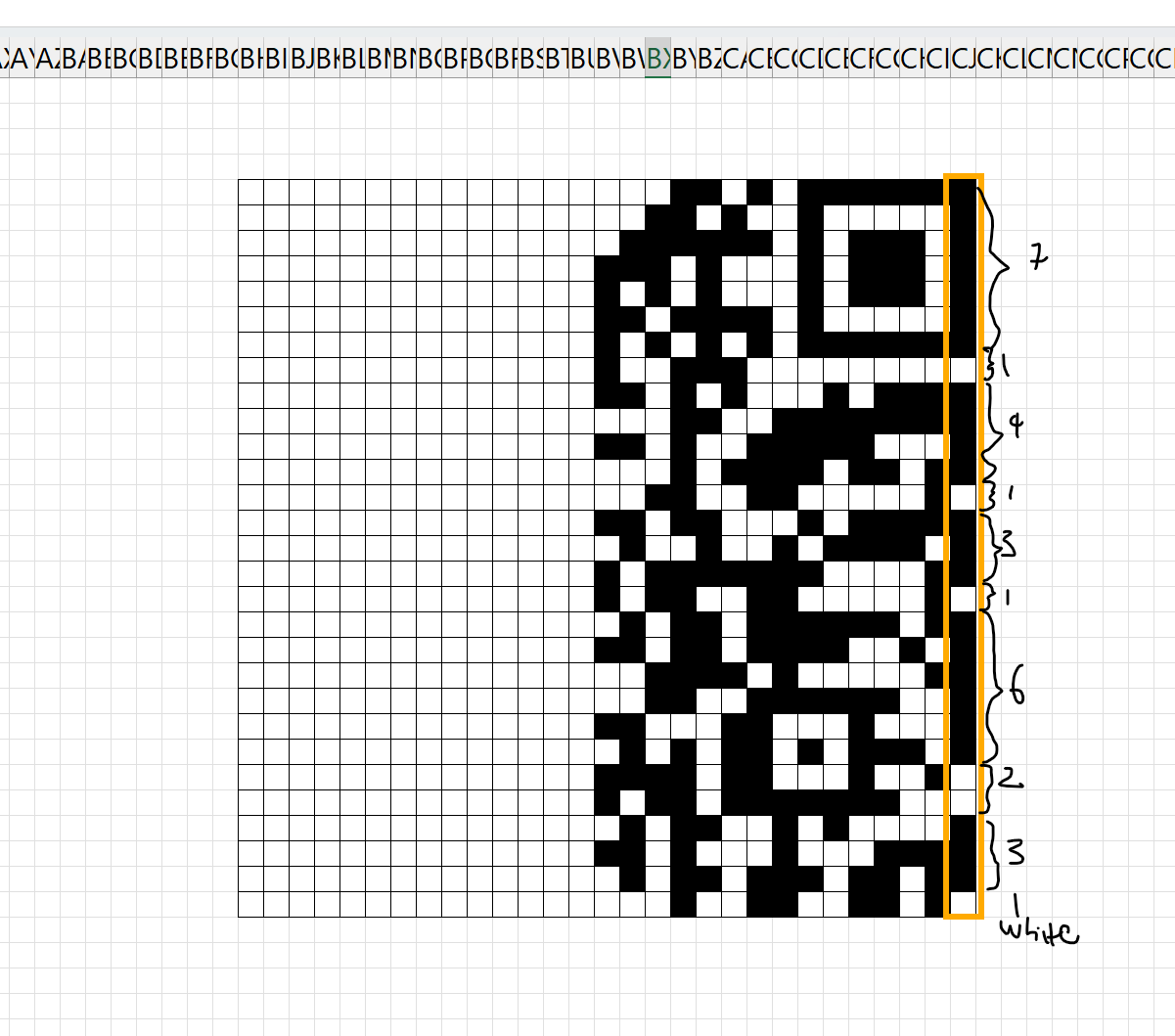
Obtaining Error Correction Level and Masking Value
From https://www.nayuki.io/page/creating-a-qr-code-step-by-step, we can see that the Error Correction Level is Low and the Bit Masking is 4! We can also refer to Thonky’s explanation for QR Mask Patterns . We can also confirm by referencing the Format and Version String TablesIt is also interesting to note that a huge majority of reed solomons ECC values are on the left hand side of the QR code that is not available for us. But as a side note, there is where we can calculate our own reed solomon code as well to recreate a scannable QR code that would not be covered in this post. We can also make use of one of the best step by step tutorial by Nayuki!
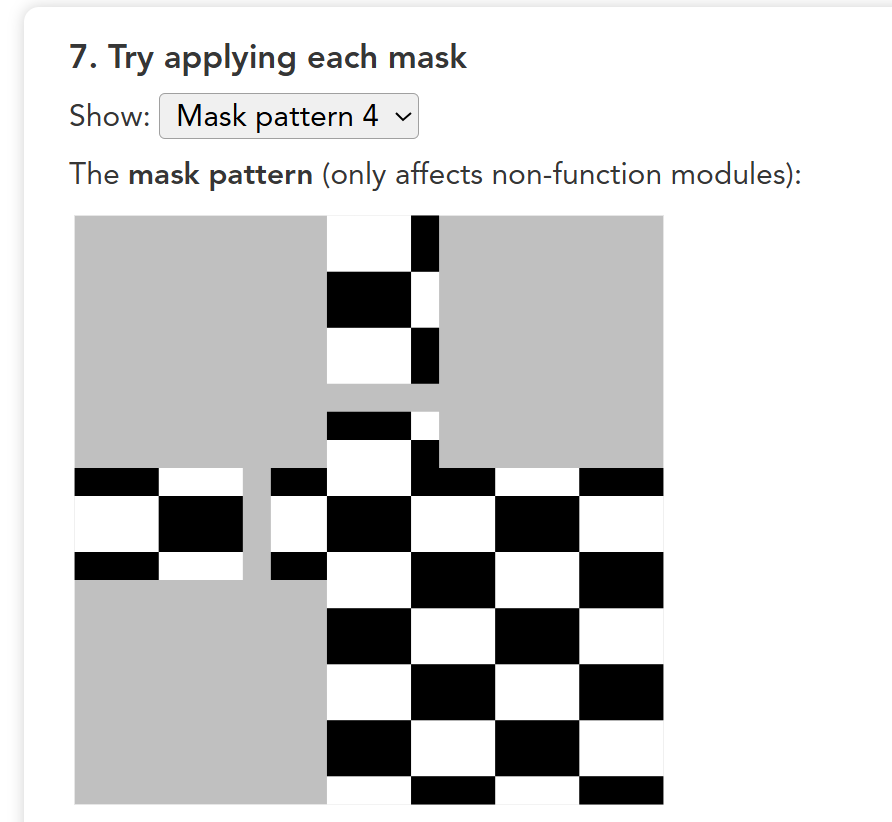
Also, we can see that the bit masking would look like this. What bit masking does is to do a bitwise xor for each byte. Black cell represent 1 while white cell represent 0. It seems also that the purpose for bit masking is also to prevent large chunks of white or blacks which can make things hard for the scanner perhaps. To reduce that, this masking aims to break that up.
Marking Immutable Regions
Note that the light blue, purple and orange shaded cells are not where data will be placed in. While the grey out parts represents the masking pattern. The orange shaded region informs us of the error correction level and the bit masking pattern.
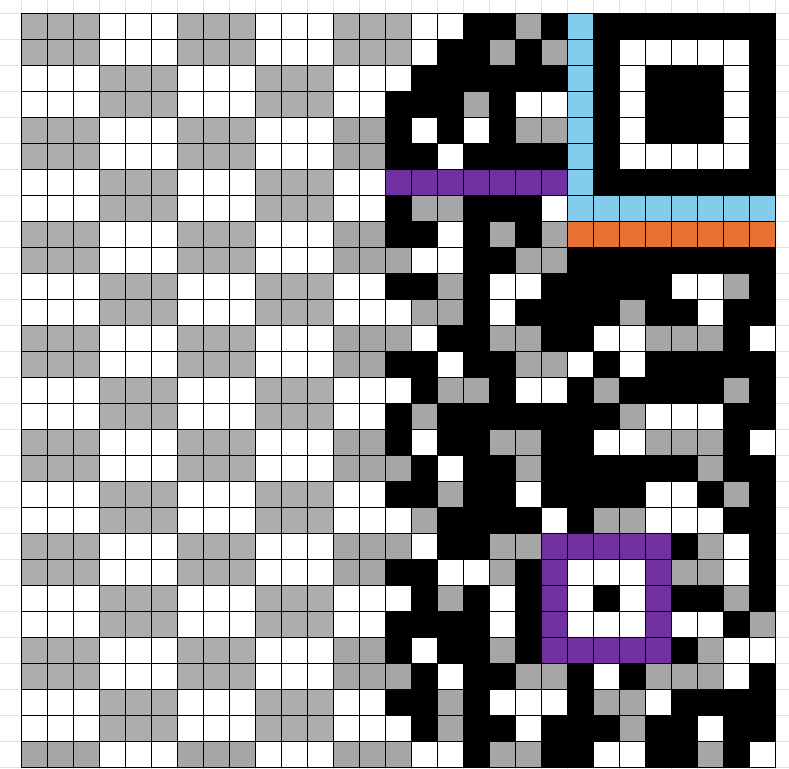
Revealing Data
To reveal the data, for those cells with:
- overlapping grey and black, we will turn it white.
- For the remaining grey without overlapping black, we turn them black
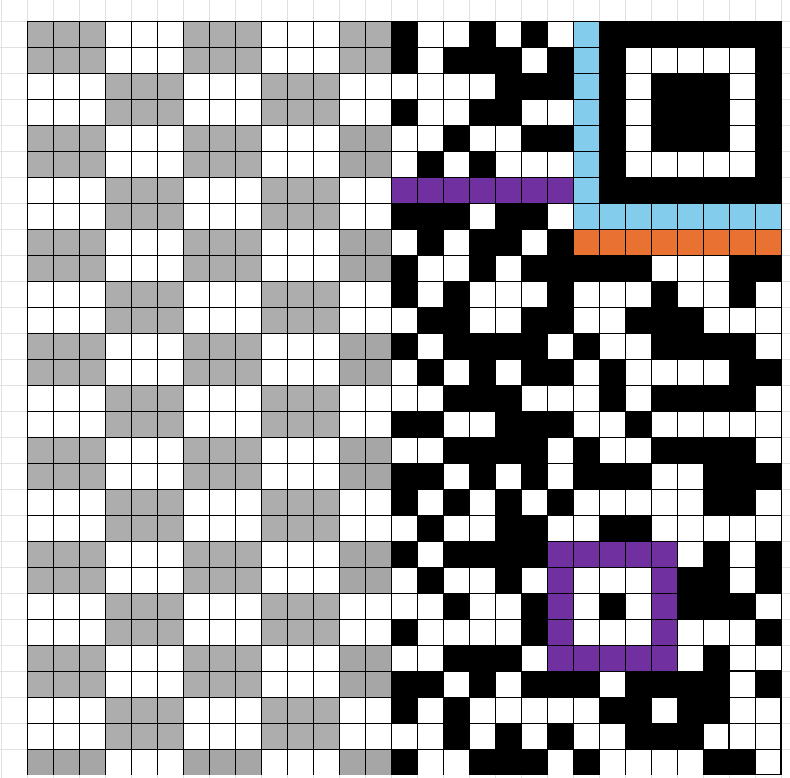
Retrieving Data
The following shows how data is retrieved
Though, the first four bits reveals encoding and the next 8 bits reveals the size (38). The rest of the data is what we are interested in. Or at least, the next 38 bytes.
Here is the example of first data byte 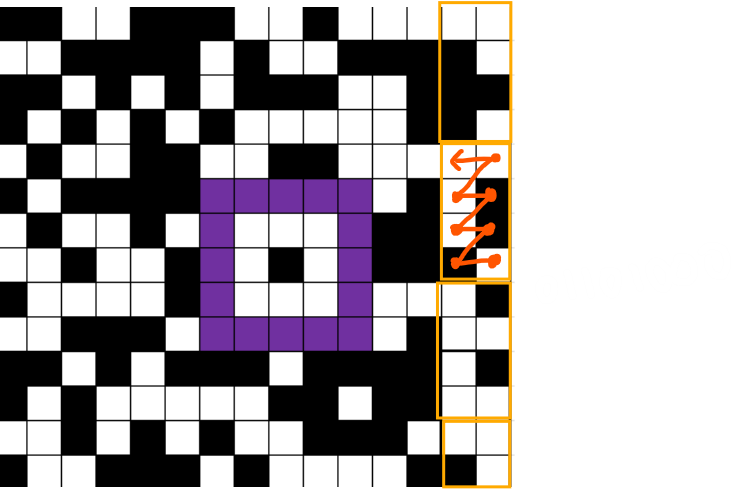 The following was extracted and placed in a python script.
The following was extracted and placed in a python script.
s = [ 0b01101000, 0b01110100, 0b01110100, 0b01110000, 0b01110011, 0b00111010, 0b00101111, 0b00101111, 0b01100011, 0b01110100, 0b01100110, 0b00101110, 0b01110000, 0b01101000, 0b01110010, 0b01100001, 0b01100011, 0b01101011, 0b00101110, 0b01101111, 0b01110010, 0b01100111, 0b00101111, 0b01100011, 0b01101000, 0b01101111, 0b01101101, 0b01110000, 0b01101001, 0b01100101, 0b00110001, 0b00110011, 0b00110011, 0b00110111, 0b00001110,]
link = ""for i in s: link += chr(i)
print("Link : " + link)print("Left : " + str(38-len(link)) + " characters")
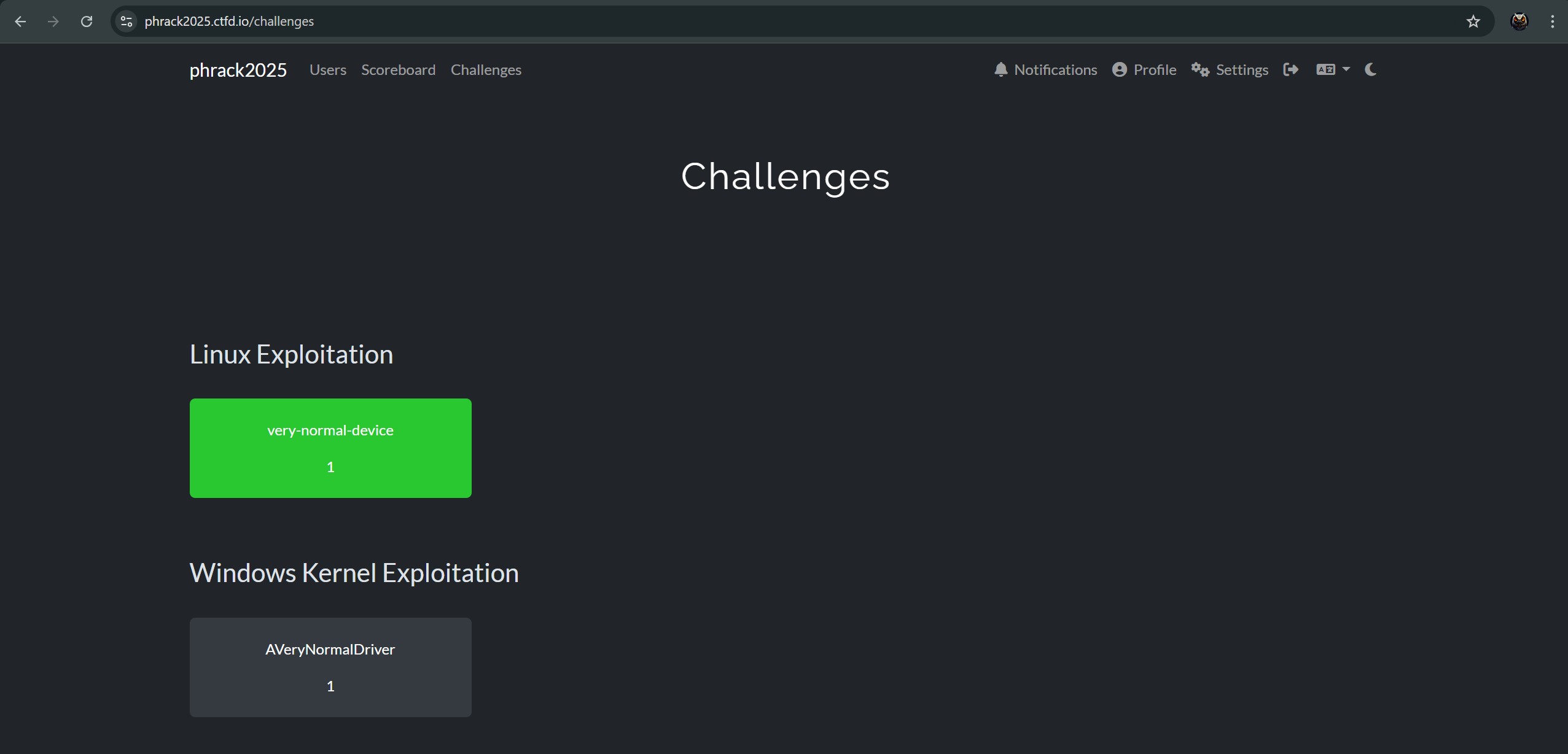
"""PS C:\Users\Owl4444\Desktop\phrackctf> python .\main.pyLink : https://ctf.phrack.org/chompie1337Left : 3 characters"""Accessing the CTF Site
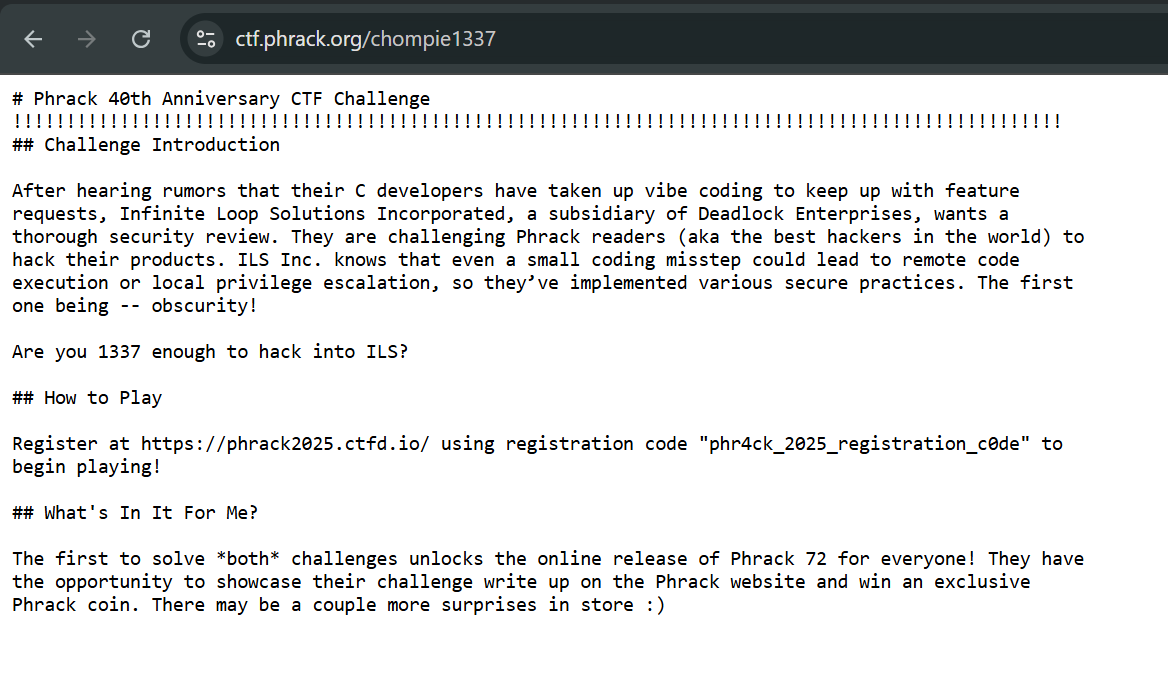
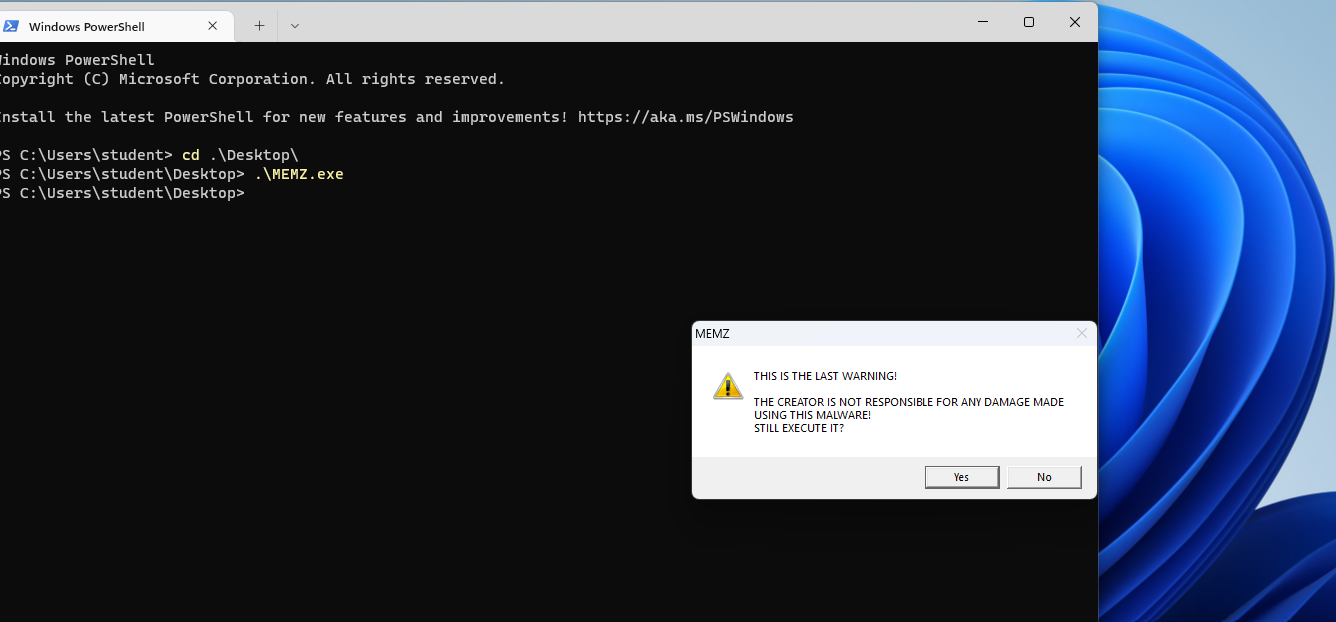
When accessing, only the Linux exploitation one is exposed. To continue on to windows kernel exploitation challenge, we will need to solve the Linux one first.